Forensics
When something goes wrong,
you need proof,
not assumptions.
Reconstruct exactly what happened in any incident: who did it, when they did it, and how they did it.
Track events in real time, recover evidence, and have complete traceability for auditing and critical decisions.
INGITE transforms investigation into certainty: more control, immediate response, and zero blind spots.
Why choose our
forensic investigation solution?
Investigate suspicious activity, preserve evidence, and respond quickly to incidents

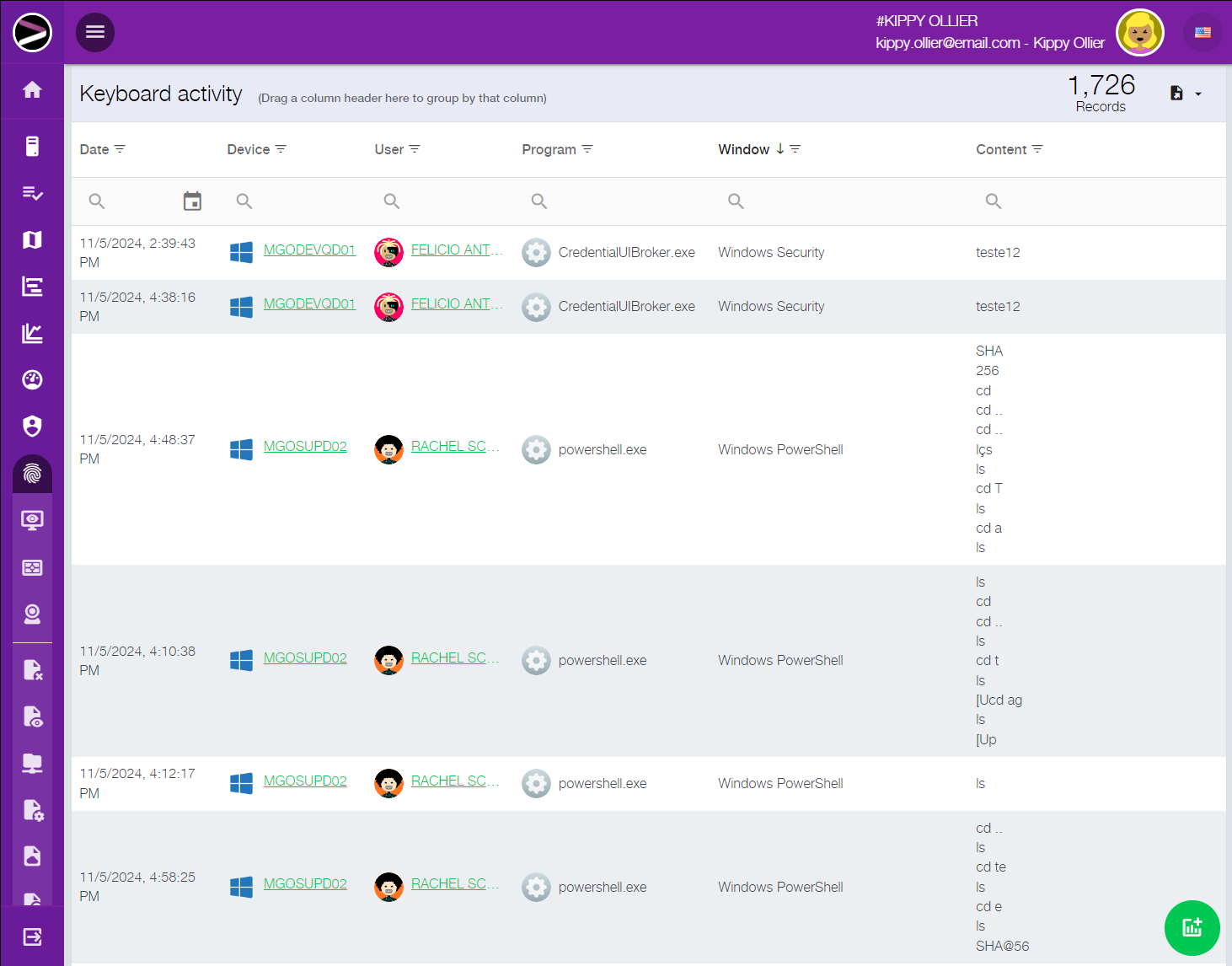
Complete traceability of actions
Reconstruct exactly what happened, when it happened, and who was involved.
The solution records activities performed on devices, allowing the company to investigate events with depth and context. This makes it possible to reconstruct actions, understand sequences of events, and reduce the time spent analyzing incidents.
Forensic evidence for audits and legal use
Generate consistent technical evidence for audits and internal processes.
The module organizes records and evidence that support investigations, audits, and legal analysis. With chain-of-custody generation and technical documentation, the company gains greater confidence in using information in formal and sensitive contexts.

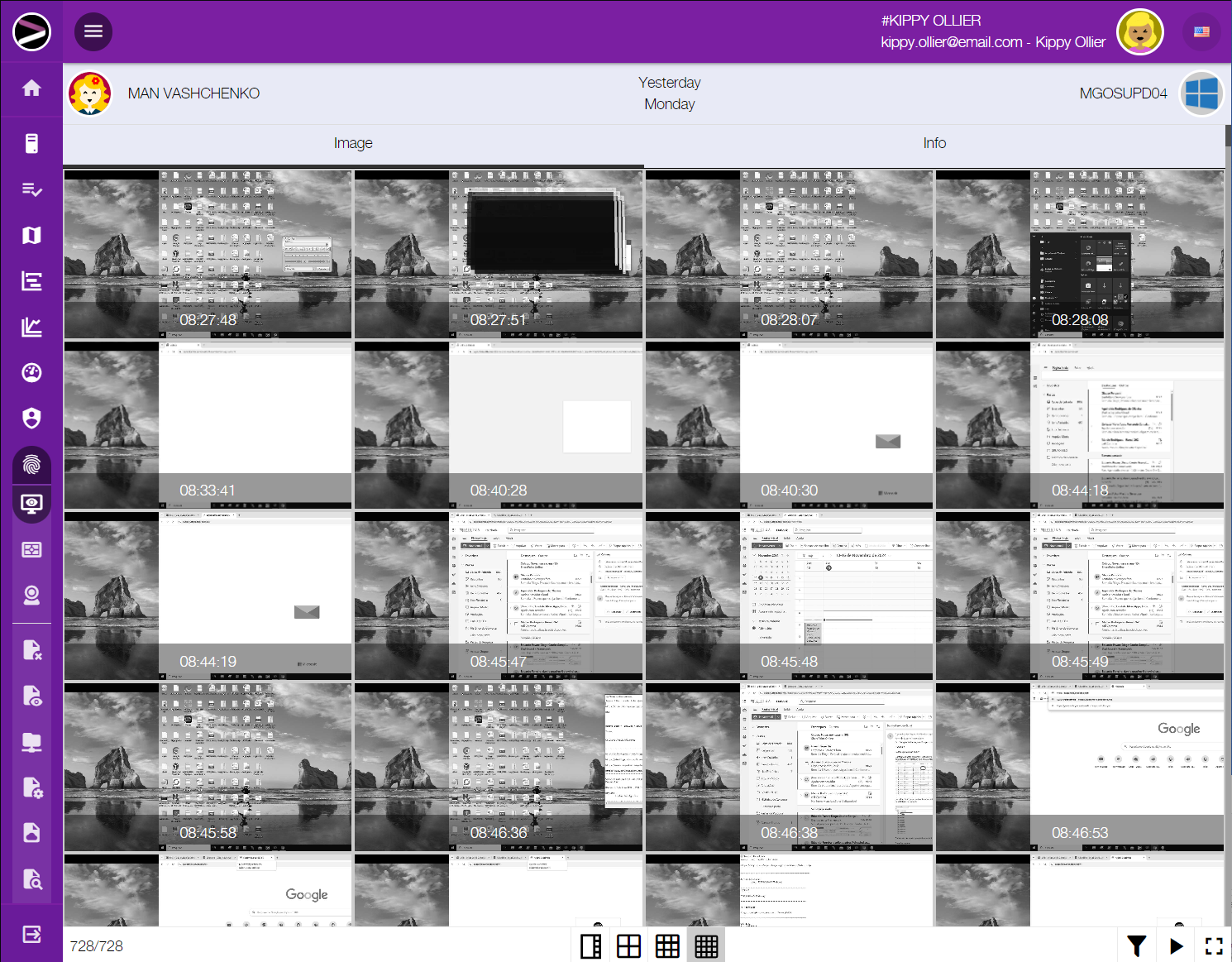
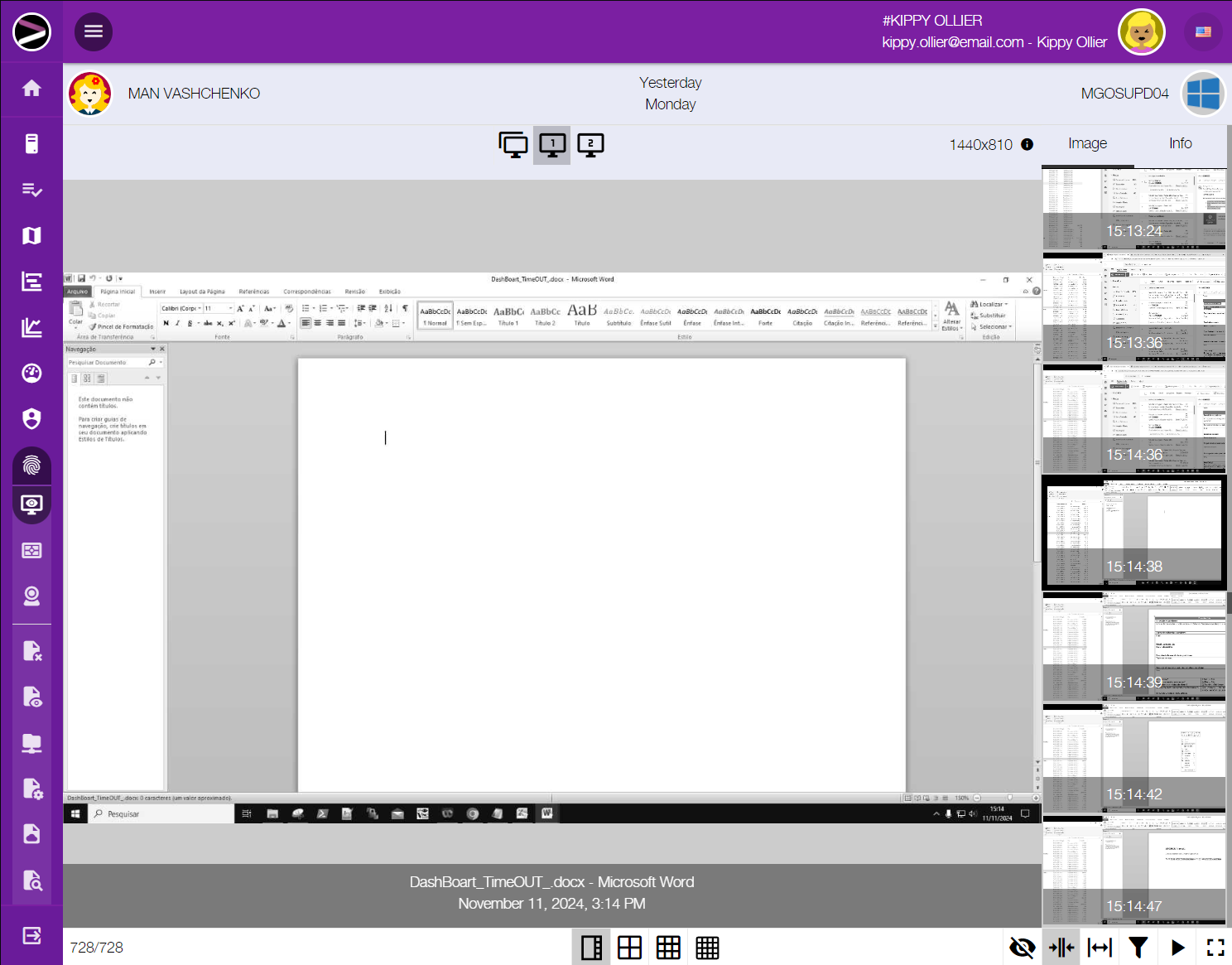
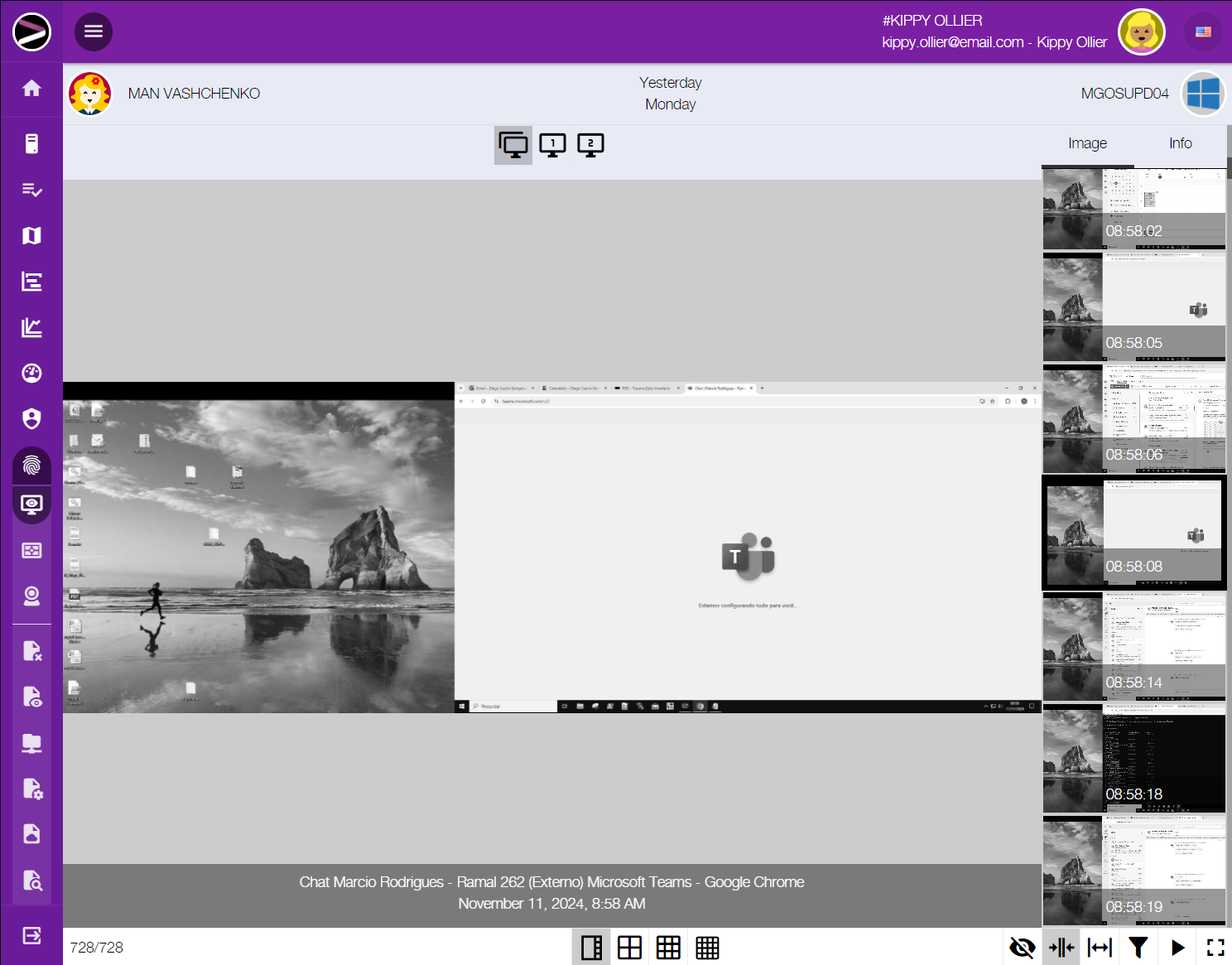
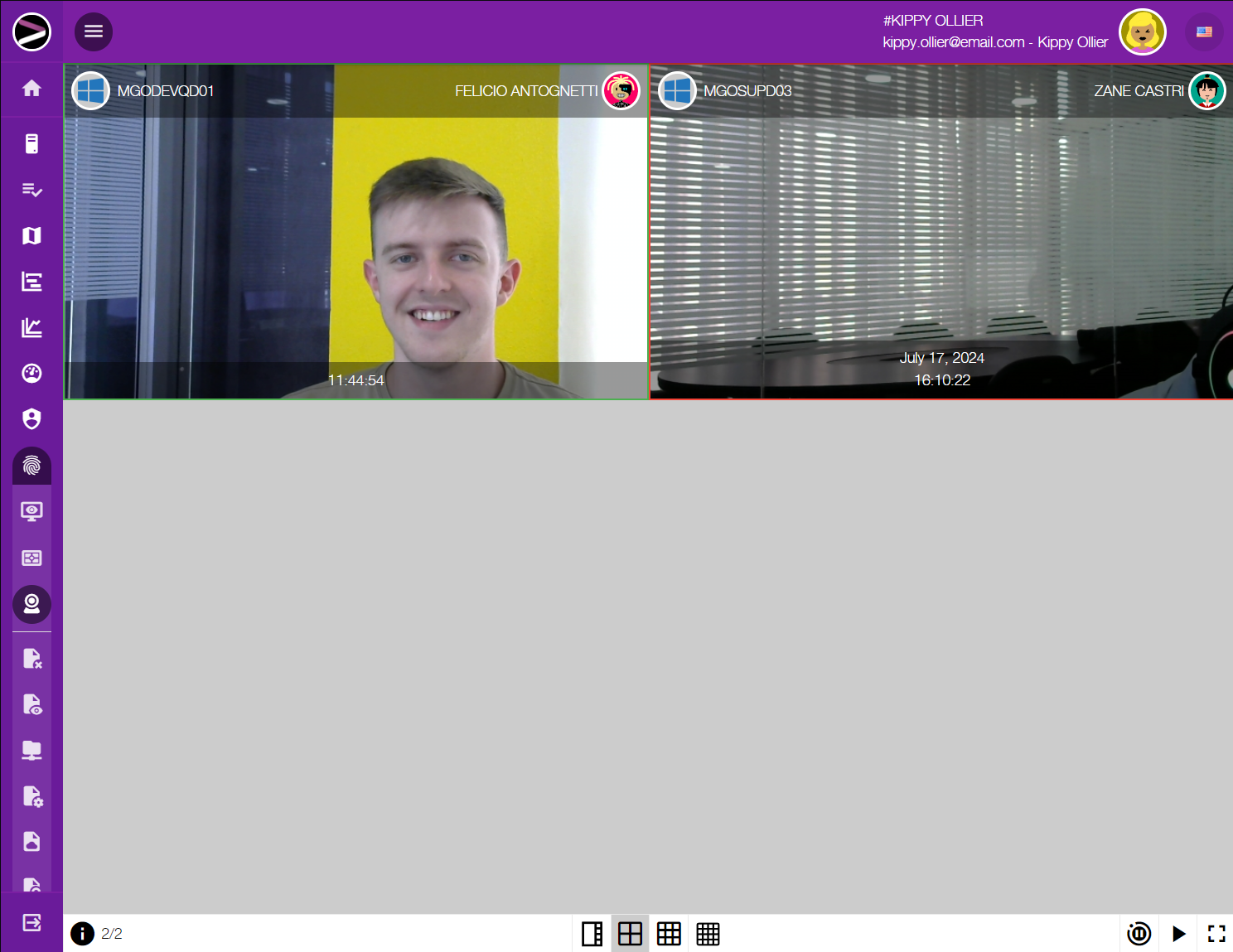
Visual playback of events
Go back in time and visualize actions performed during an incident.
With recording and playback capabilities, teams can visually review what happened during critical moments. This accelerates analysis, reduces ambiguity, and improves understanding of complex incidents.

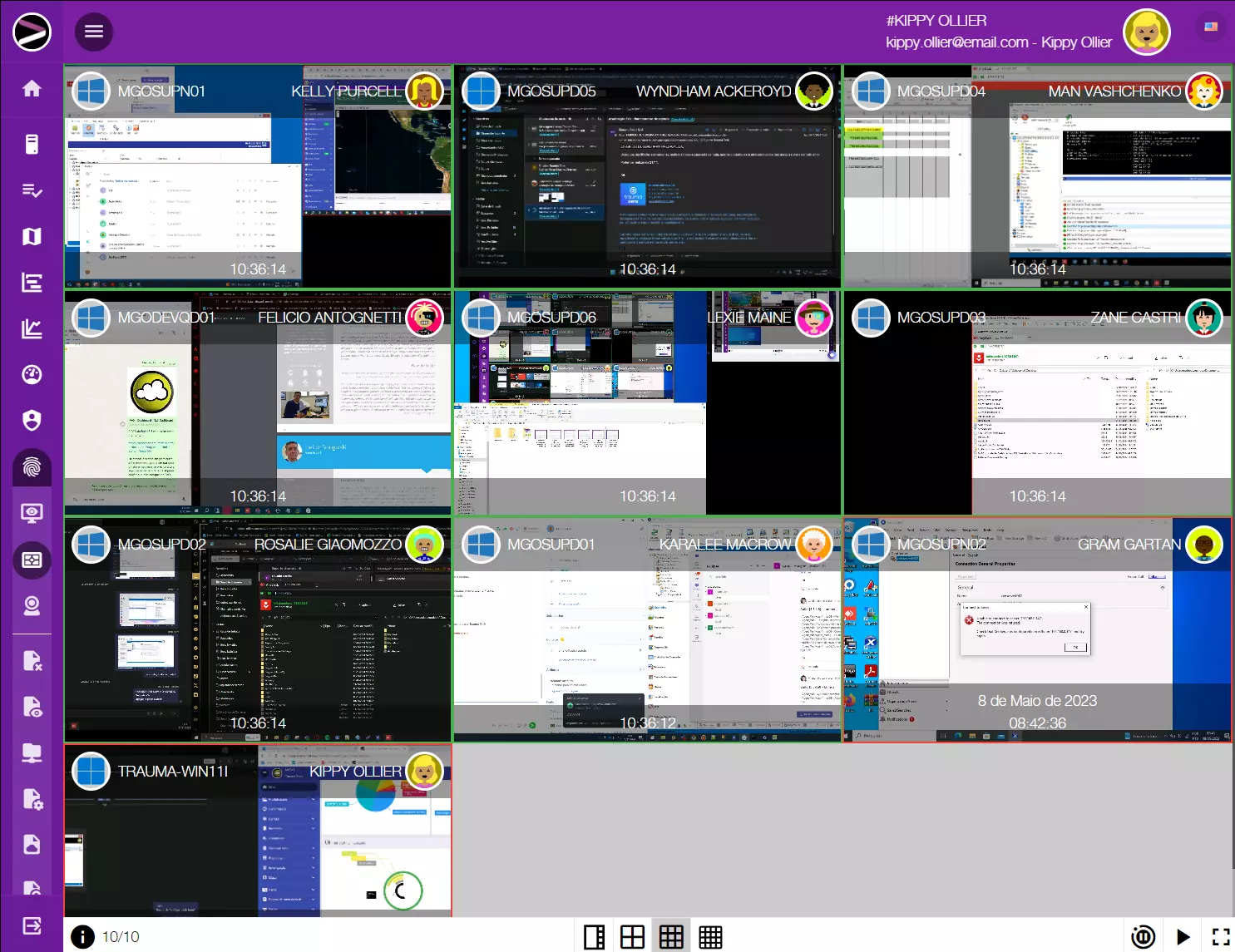
Real-time investigation with faster response
Capture evidence as events happen for faster decision-making.
The solution enables trigger-based monitoring to capture evidence during suspicious activities. This increases responsiveness and improves the ability to act quickly in cases of fraud, misuse, or security incidents.

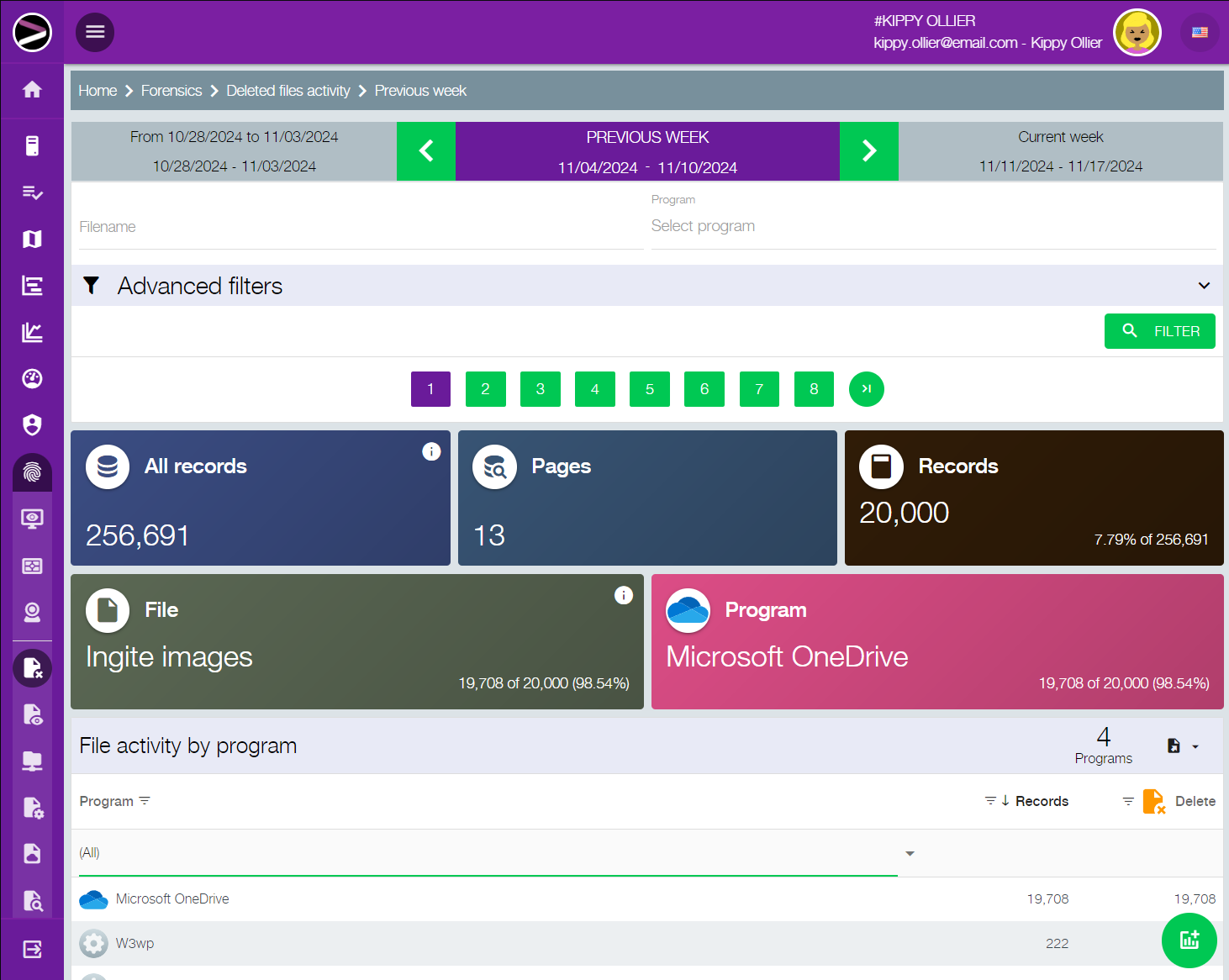
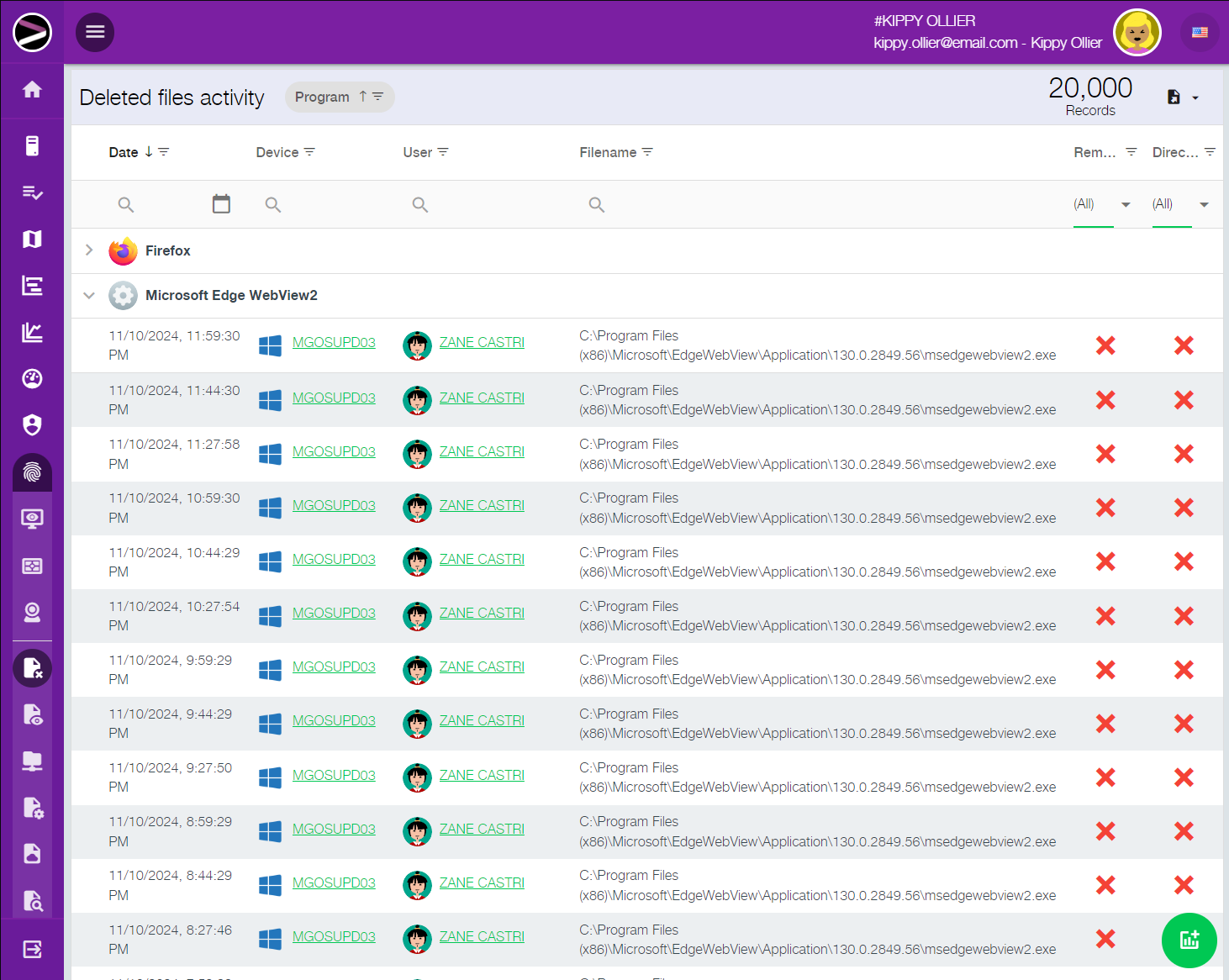
Recovery and reconstruction of critical data
Recover files, traces, and key data even after deletion or modification.
The module provides capabilities to reconstruct files and recover relevant data for investigations. This helps minimize losses caused by deletion, unauthorized changes, or attempts to hide strategic information.

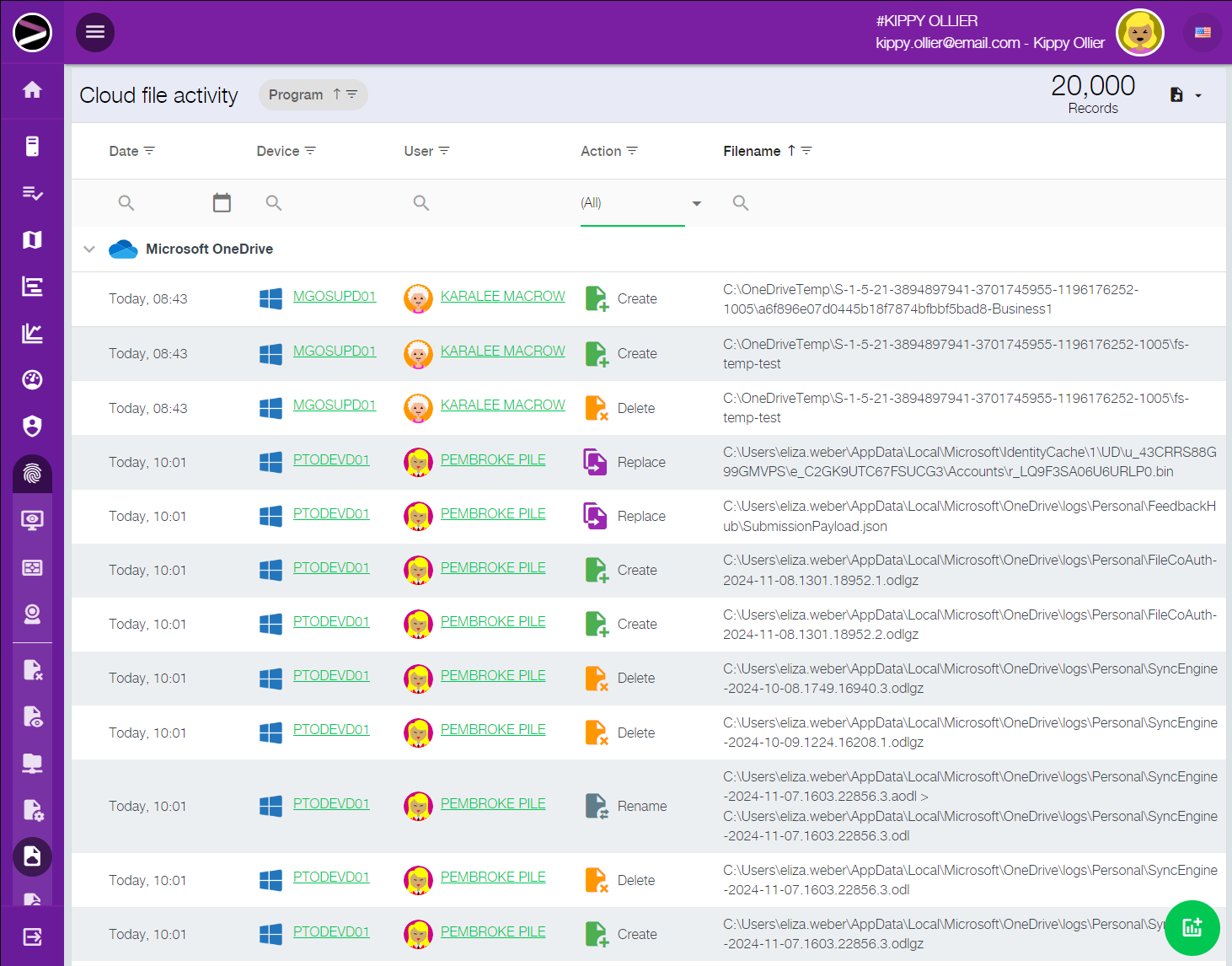
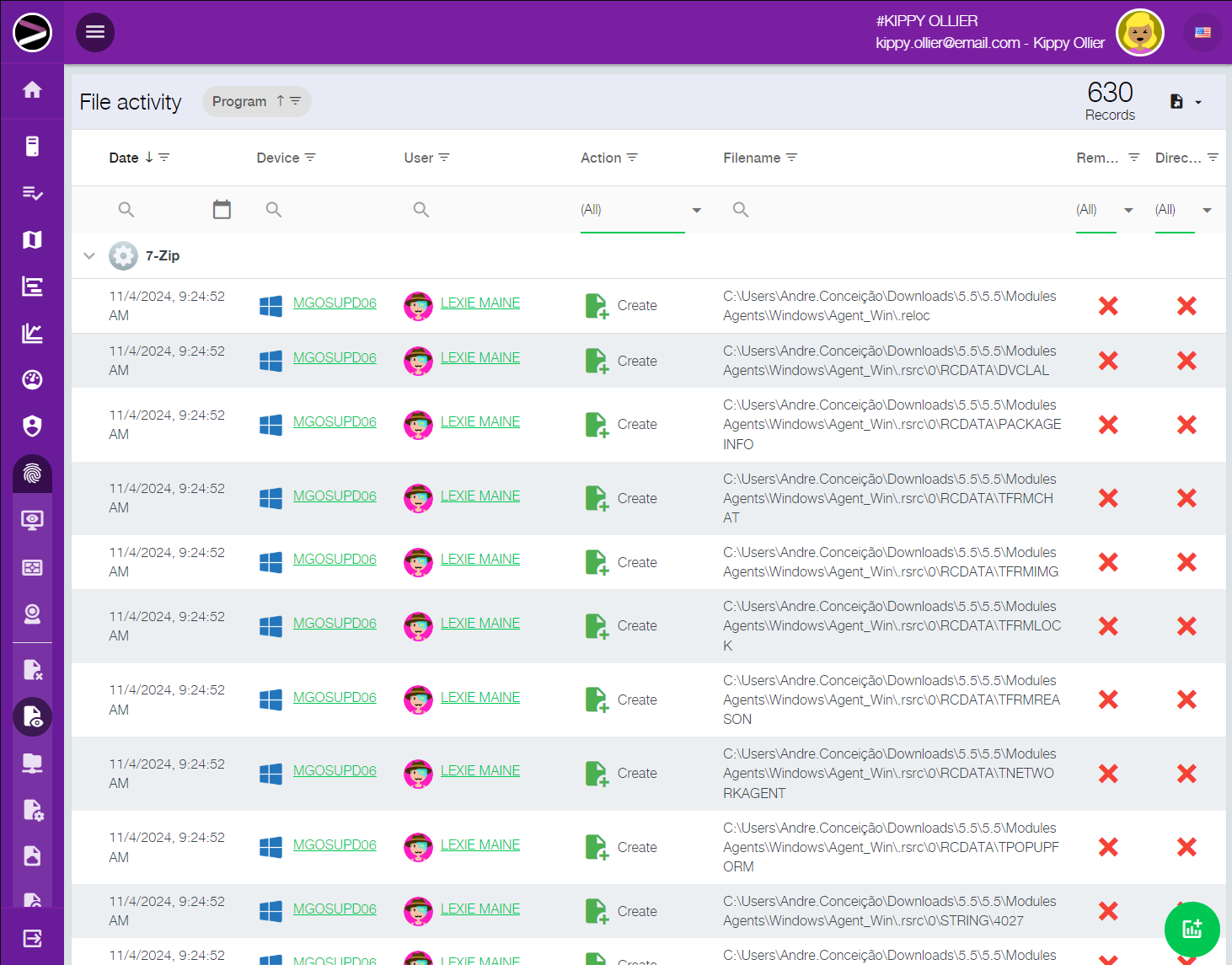
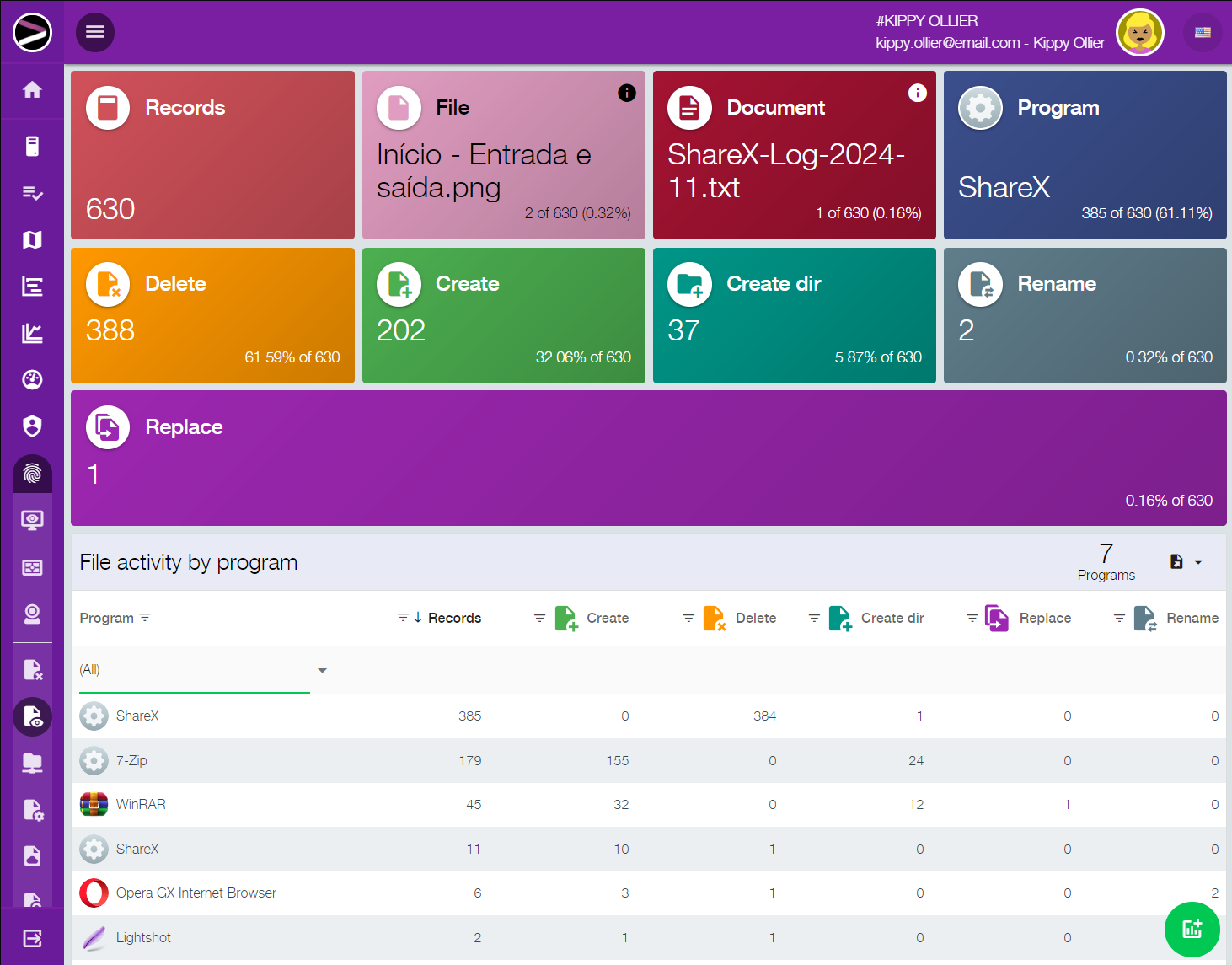
Precise identification of changes and deletions
Know who created, modified, moved, or deleted files and folders.
The platform tracks changes in files and directory structures, allowing clear identification of the origin of critical actions. This strengthens accountability and reduces investigation time.

Protection against data loss and misuse
Reduce risks of data leaks, deletion, and misuse of strategic information.
With detailed traceability and reconstruction capabilities, the solution improves the company’s ability to detect and respond to data misuse. This helps protect valuable digital assets and reduce operational and financial impact.

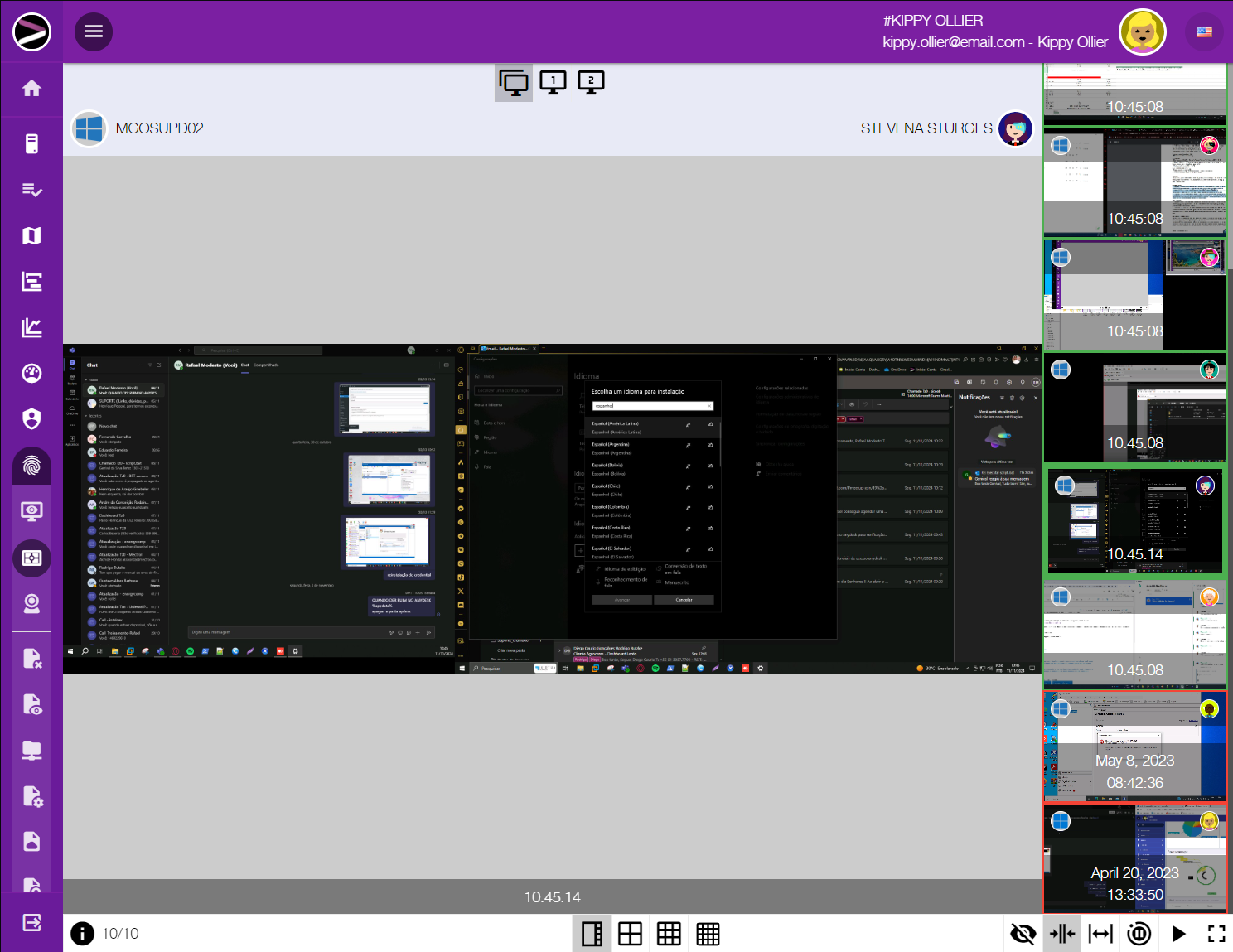
Investigation across applications, web, and cloud
Audit actions across desktop systems, web apps, and cloud services.
The solution expands visibility into activities performed in corporate applications, browsers, and cloud environments. This simplifies investigations involving access, data movement, and usage across different operational layers.

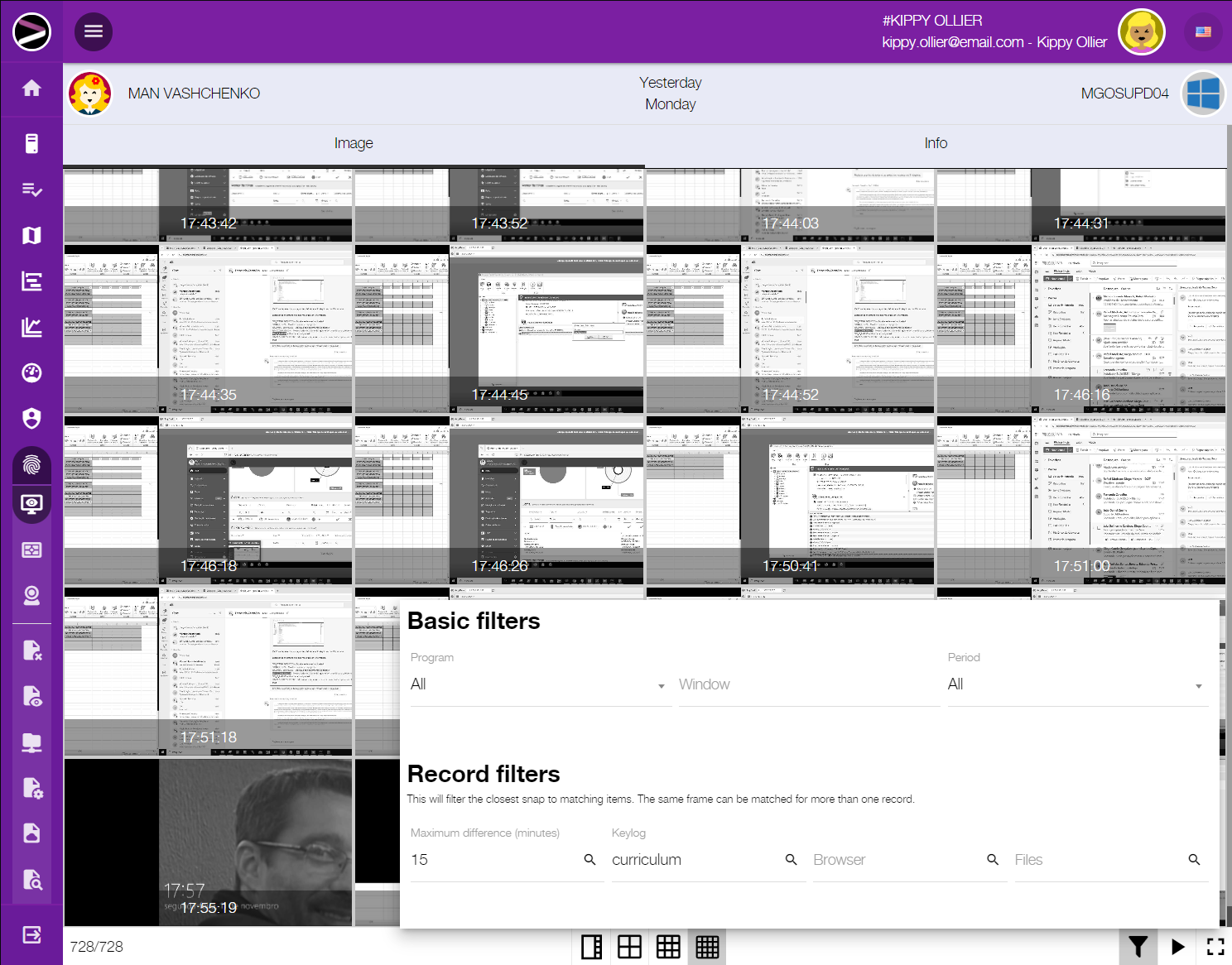
Fast search for evidence and specific events
Quickly locate relevant information during investigations.
The module allows searching records, events, and activities using multiple criteria, speeding up the identification of important evidence. This reduces manual effort and makes investigations more efficient and objective.

A solid foundation for complex incident decisions
Make faster decisions with reliable data in critical situations.
By centralizing evidence, records, and operational context, the solution supports decision-making in complex incidents. This improves response capability and reduces reliance on assumptions in high-pressure scenarios.
Product gallery