Security
Your security doesn't fail
because of a lack of rules.
It fails because of a lack of control.
Apply policies that actually work: block access, control devices, and react to threats in real time.
Protect your environment inside and outside the network, with complete visibility into risky behaviors and breach attempts.
INGITE transforms security into execution: more control, less exposure, zero operational gaps.
Why choose our
security solution?
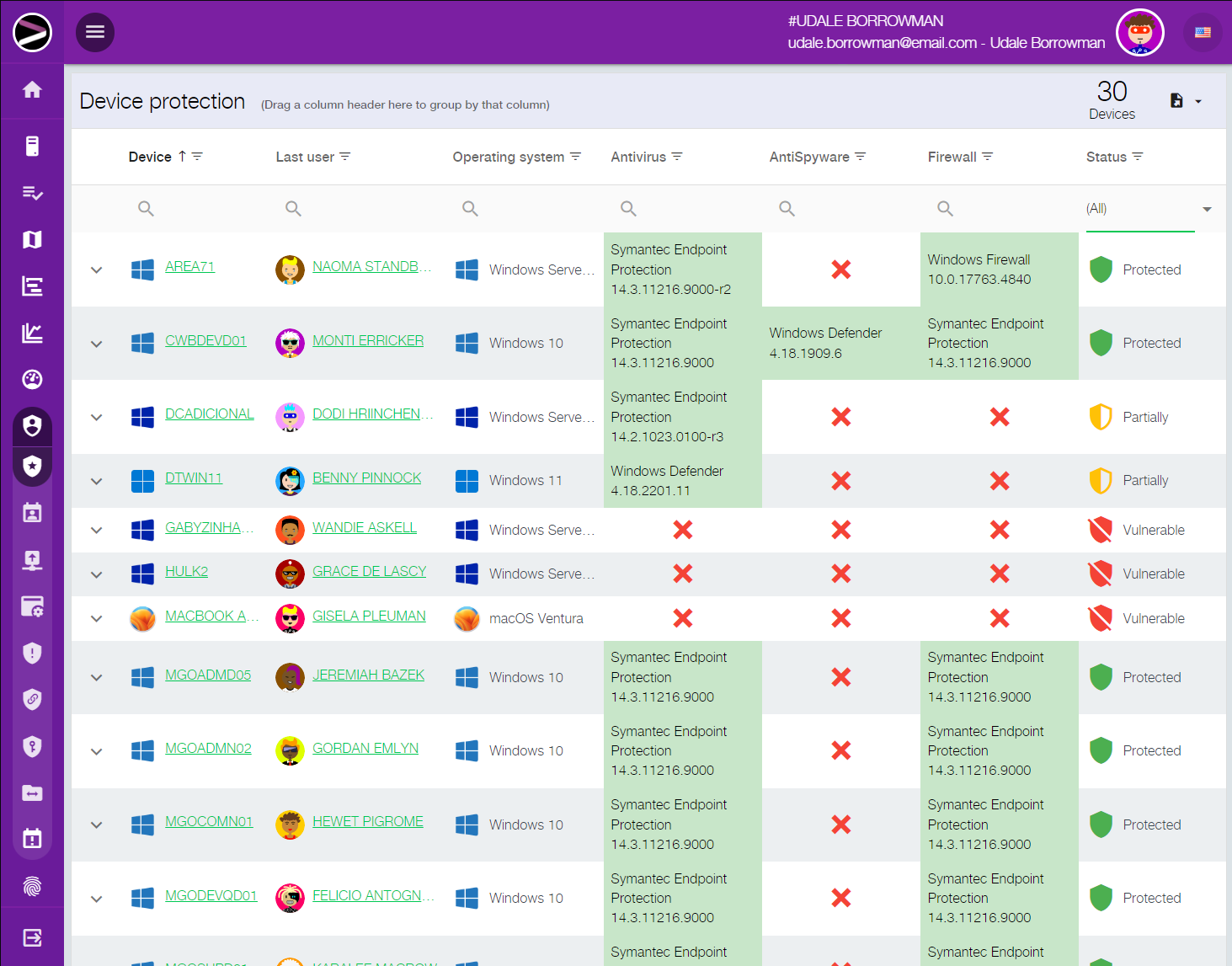
Ensure policy compliance and protect your company's technology environment

Security policies enforced in practice
Ensure real enforcement of your company’s security rules.
The solution allows you to create and enforce security policies that define how, when, and which resources each user can access. Instead of relying only on internal guidelines, your company gains effective control over the use of its IT environment.

Smart access and resource blocking
Restrict access to software, hardware, websites, folders, and files with precision.
The platform allows blocking or granting access to specific resources based on user, group, or device profiles. This reduces unnecessary exposure, limits improper behavior, and strengthens day-to-day protection of the corporate environment.

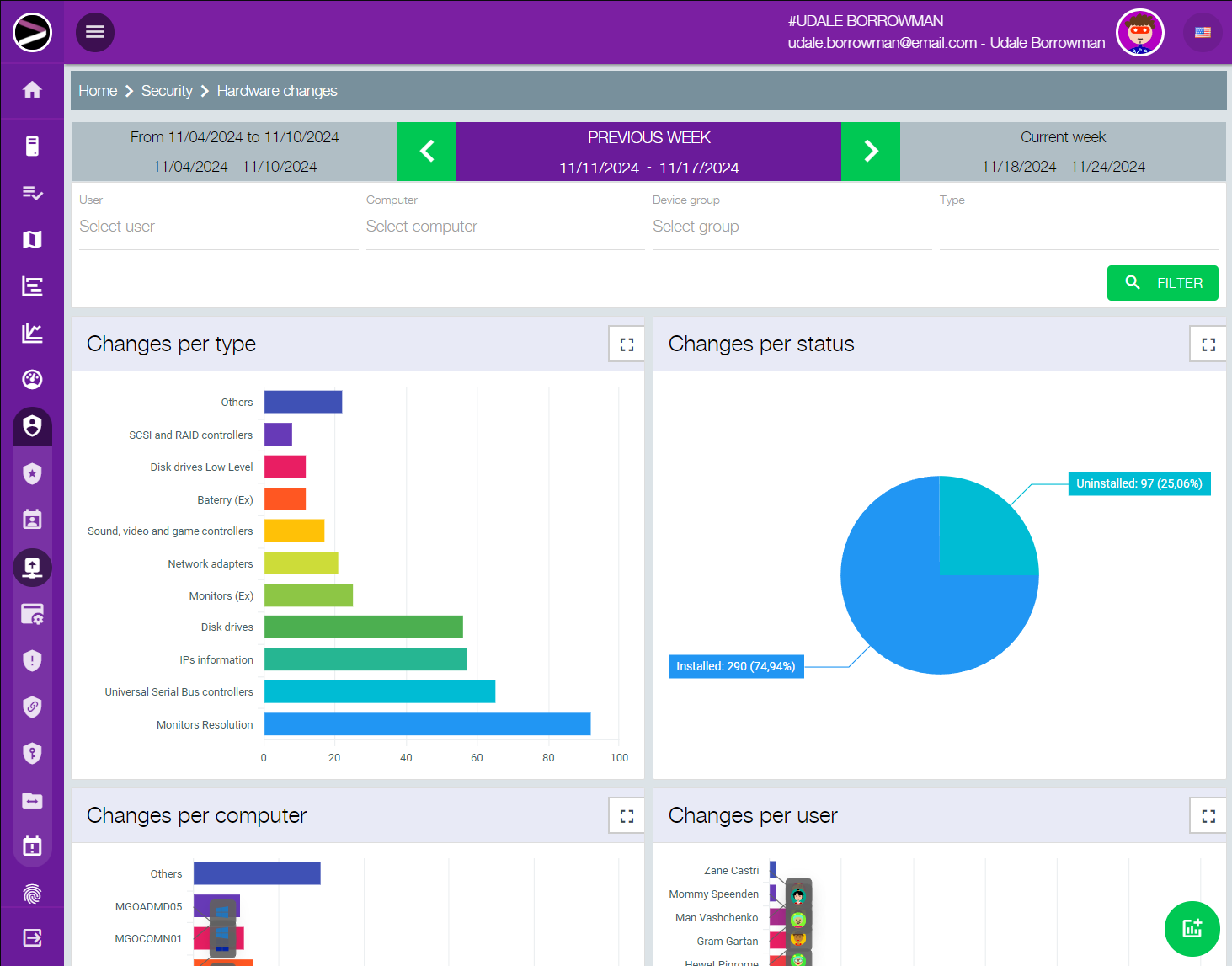
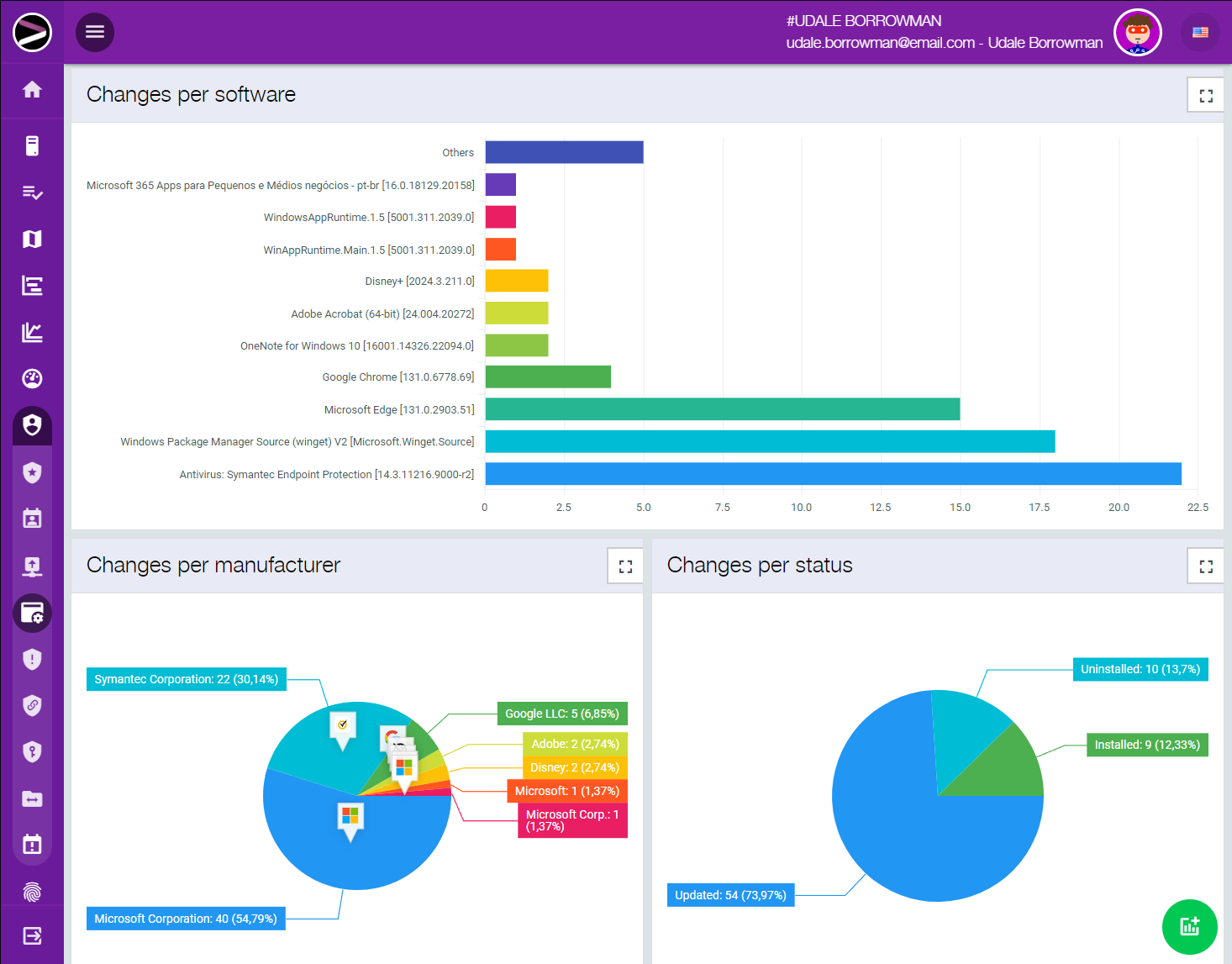
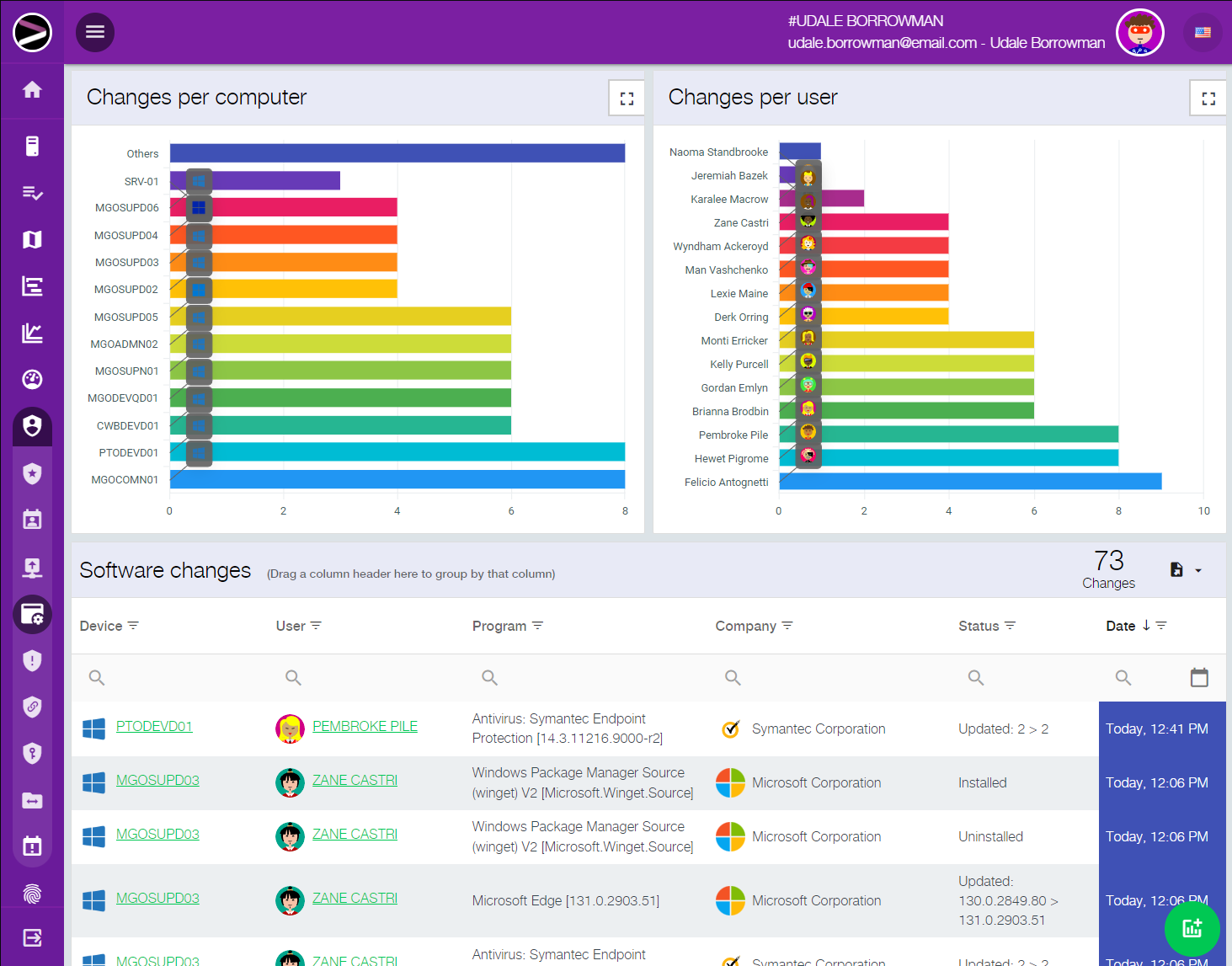
Real-time alerts and visibility
Receive immediate alerts about suspicious actions and environment changes.
Whenever relevant changes occur in hardware, software, or policy violations are attempted, the system generates real-time alerts and security reports. This accelerates response time and reduces the gap between incident and corrective action.

Protection beyond the corporate network
Keep security policies active even on devices outside the company network.
The module continues to enforce security policies even when devices are outside the corporate network. This is essential for remote work, field teams, and distributed operations.

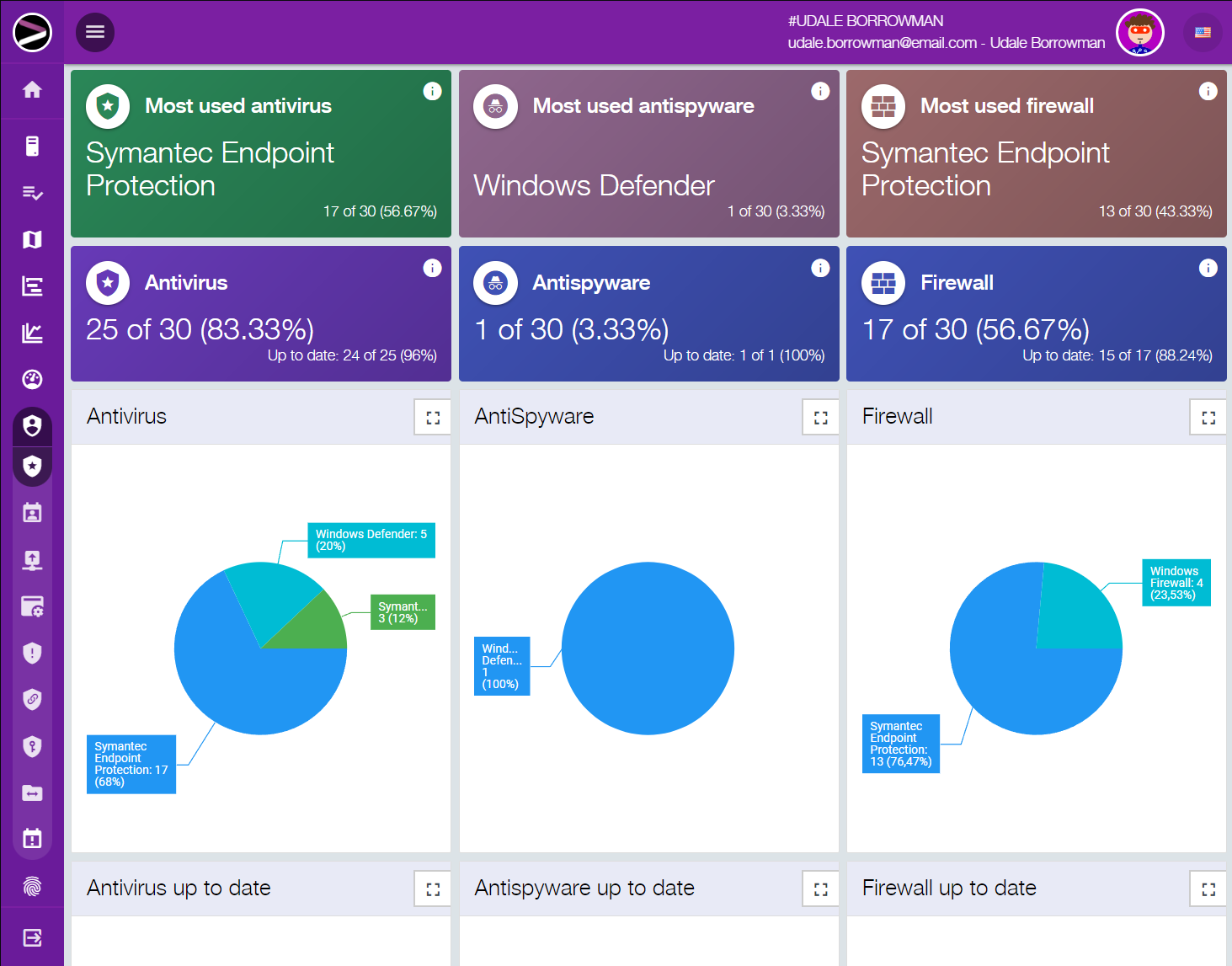
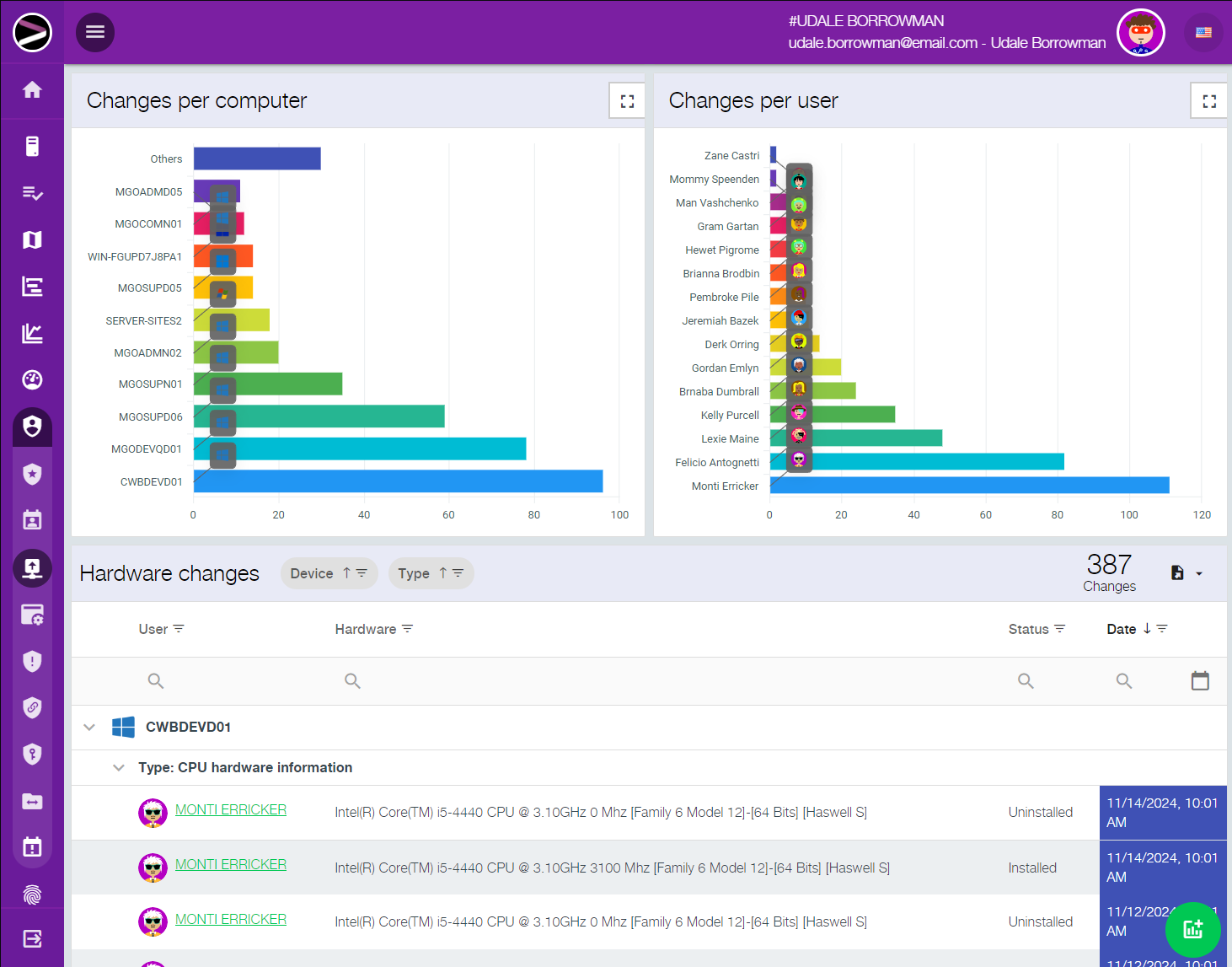
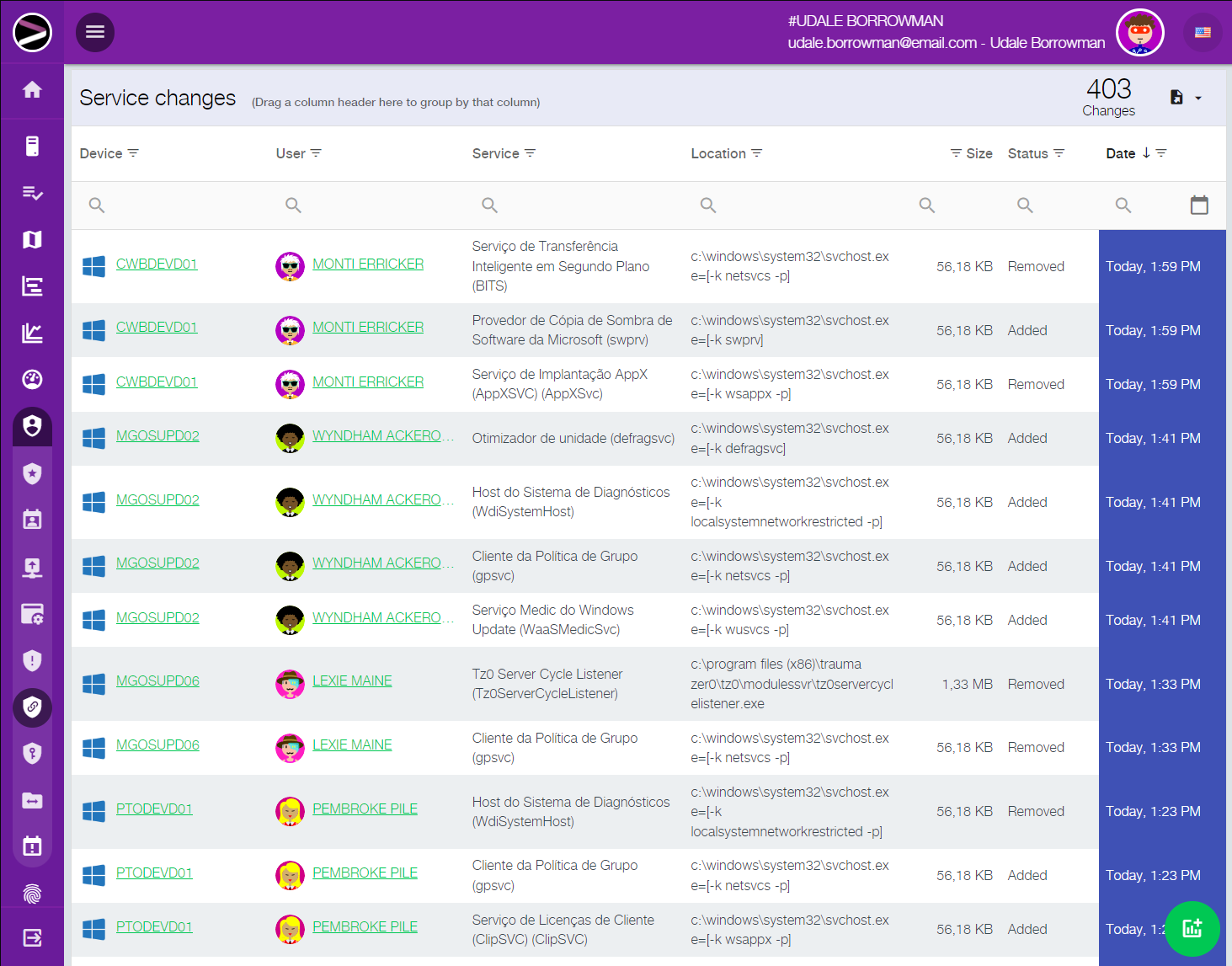
Hardware change control
Detect and prevent unauthorized hardware and peripheral changes.
With hardware snapshot capabilities, the solution ensures that workstations maintain their authorized configuration. Unauthorized peripherals, device connections, or component replacements can be blocked and reported instantly.

Prevention of fraud, loss, and misuse
Reduce risks of theft, tampering, and unauthorized equipment usage.
The platform increases environment traceability and helps identify suspicious situations involving removable devices, laptops, tablets, printers, and other vulnerable assets. This strengthens asset control and reduces exposure to fraud and loss.

Application-layer firewall control
Define which applications can access critical files and data.
The module allows creating rules so that only authorized applications can access specific files or databases. This reduces the risk of data copying, tampering, leakage, or misuse of strategic company information.

Evidence for audits and investigations
Generate reports that prove violations and risky behavior.
Users who attempt to bypass policies have their actions recorded in security reports. This creates concrete evidence for audits, internal investigations, and management decisions.

Integration with native Windows policies
Extend control using built-in Windows security features.
Integration with native Windows policies allows you to block or allow resources by user, group, or device. This simplifies administration and ensures consistent rule enforcement both inside and outside the network.

Work schedule control with reduced labor risk
Control usage hours and generate evidence to reduce labor liabilities.
The solution allows defining access schedules, tracking absences, and automating logoff or shutdown at the end of working hours. This improves traceability, strengthens control over off-hours usage, and helps reduce exposure to labor risks and liabilities.
Product gallery